Tag: the basics
-

Understanding permissions in windows
In this article, we are going to discuss the permissions in windows. I am not going to in-depth analysis but what I will try to do is to give an overview of how windows handle permissions. This is going to help you in privilege escalation of windows. These are the list of things that we…
-
X-Frame Options Missing, don’t let your button miss the click
XFO also know as X-Frame Options, if you are a web developer or aspirated to be one, security analyst then you might be hearing about X-Frame options. If you don’t know what it is and what is its role in security, then just hold on to the article. In this blog, I will be discussing…
-

Quick checklist while you are developing any application for DevSecOps
DevOps is the thing that every organization is looking up to from the last half-decade and almost all tech giants are following that even there are startups which made millions providing solutions on DevOps but then what’s next? What’s next big thing after DevOps and then it comes DevSecOps. What is DevSecOps? DevSecOps is nothing…
-

Memory Segmentation In a Nutshell
Memory segmentation is a place where all the things happen while any program is running. Memory is divided into several segments and in this article, we are going to discuss them Usually compiled program memory is divided into 5 segments text data bss heap stack
-
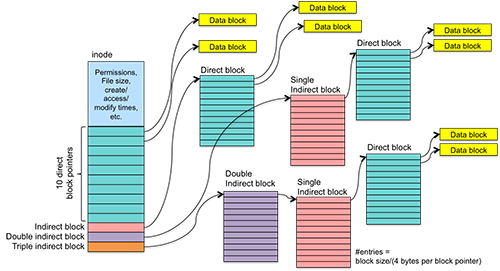
What is UFS – Unix File System and ext Family
Knowing about Unix File System is important because it is the file system that is used by Linux distros and it is one of the most used kernels out there. XFS, JFS and many more file systems are like UFS so if you know about this file system you can cover other file systems based…
-

NTFS File System Basics and Structure
Even though FAT is one of the widely used file system it lacks many features. When Windows is about to launch Windows NT, which is sever based operating system they want to launch a new file system that can have capabilities that FAT doesn’t have.
-
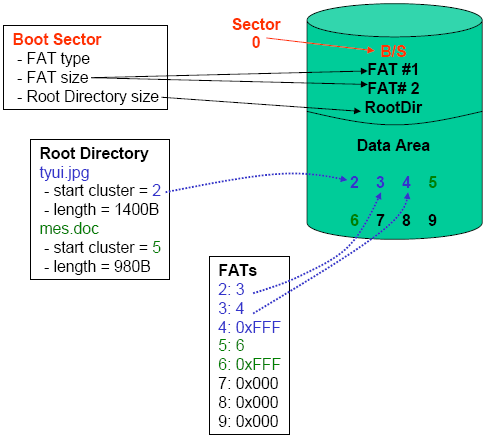
Everything a Security Analyst need to know about FAT File System
For understanding disk-based forensics we need to know about each file system, how it works and what it’s made up of. In this article we will share you everything that we know, and you should know about FAT FAT stands for File Allocation Table. It is one of the most widely used file system…
-

Everything you need to know about File System Basics as a Forensic Analyst
What operating system do you use? Linux, Windows or Mac? Whatever the operating system you are using it doesn’t matter. You will be storing files in it. Every operating system uses their kind of file system. Windows uses NTFS, Linux uses FAT and there are different types of FAT systems too. So, to create any…
-
Secure way to access dark web on android
Everything is on mobile and when we analyze the traffic we are getting to internet most of the sources are from mobile. Every web application is making their mobile apps. But for most of the people who wants to access dark web their first choice is desktop or laptop. To make it handy I have…
-

11 Insane Things You Can do with Batch Programming
Howdy! In this article we are going to learn how to create some virus programs with the help of batch scripts. Let’s get on to some grey shade of the Batch Programming. Wait, wait, what is this Batch Programming first? Don’t worry, by the end of this article you are going to learn what is…
